A Post-Quantum Cryptography safe algorithm. Deemed to be a sbustitution-permutation network. 128 bit Symmetric Block-Cipher.
- The key is constructed out of 64 bits Takes a message and a key. The key can be 128bits, 192bits or 256bits. The message must be
Concepts
Attacks
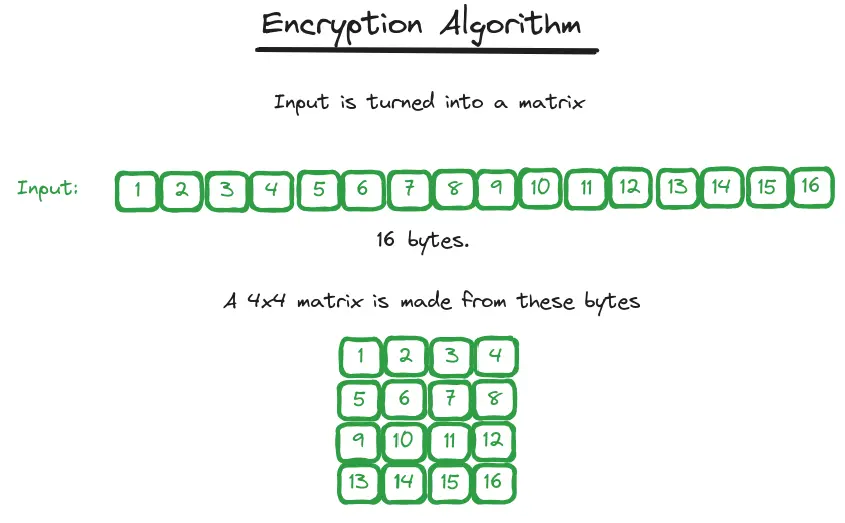
Encryption Process
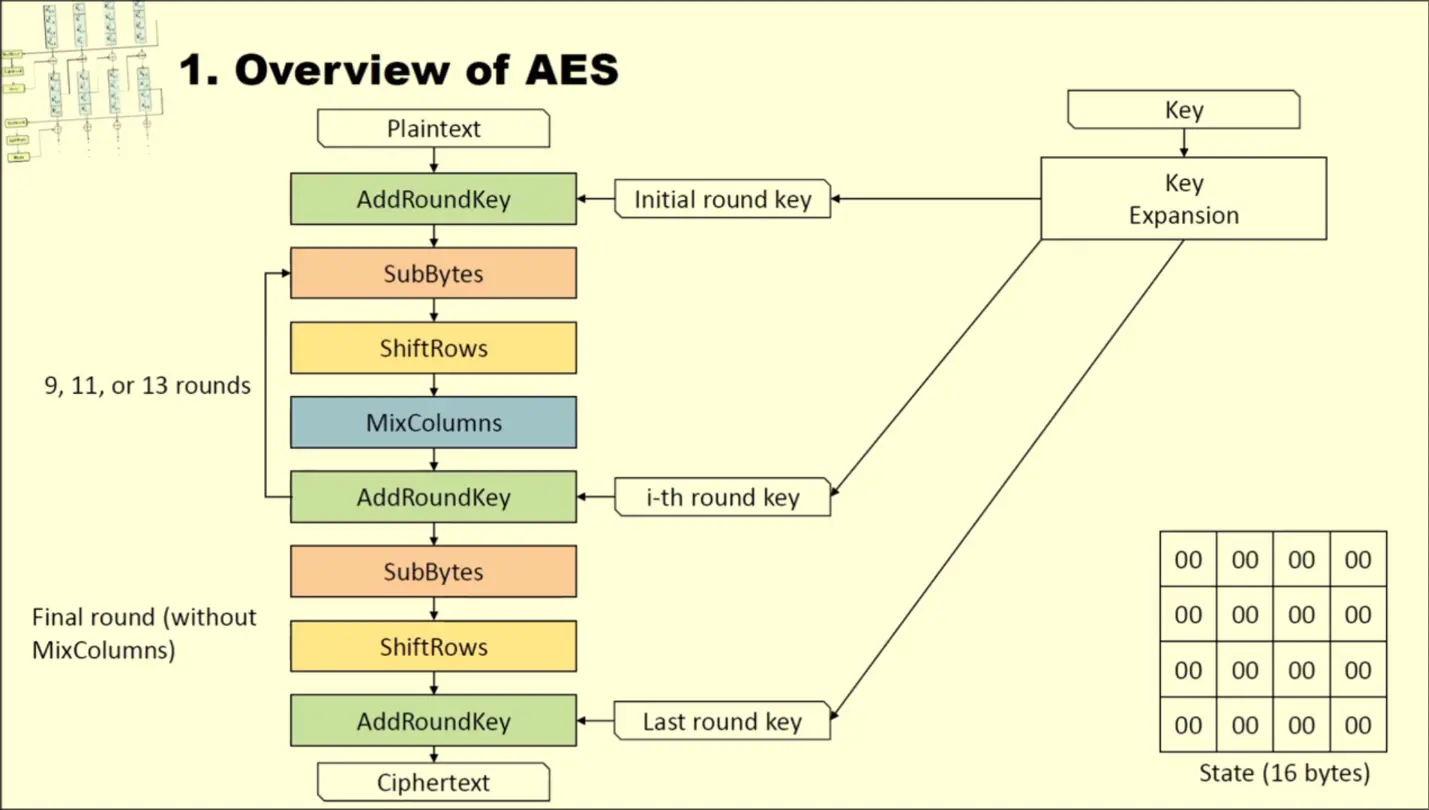
- Our input is split into 16-byte block, each block is converted into a Matrix
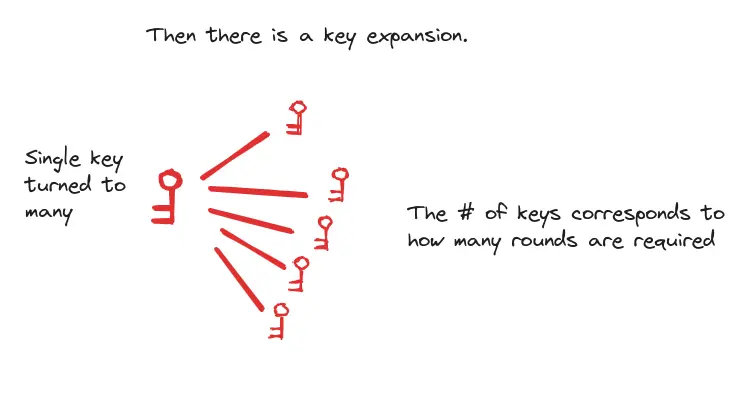
- Key Expansion: The 16-byte key segments is turned into number of Round Key which are also matrix
- if AES-128
- if AES-192
- if AES-256
- Set the current state to the 16-byte input matrix
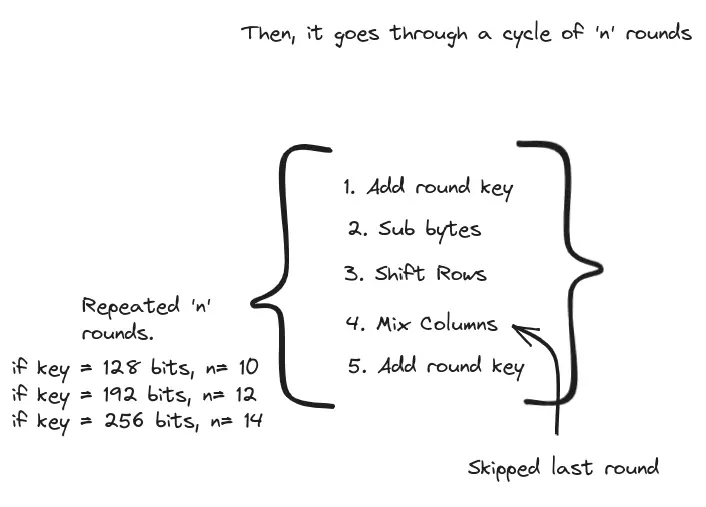
- Repeat for rounds:
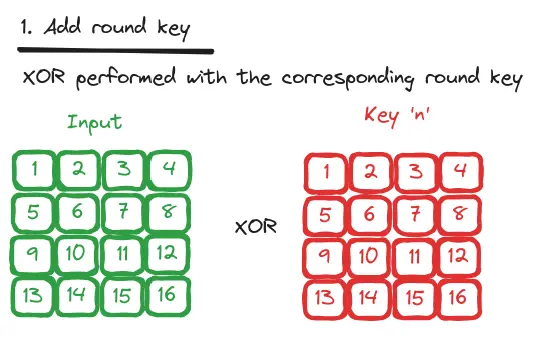
- AddRoundKey: XOR current state with current round key (Every cell of state, XORed with corresponding cell in round key)
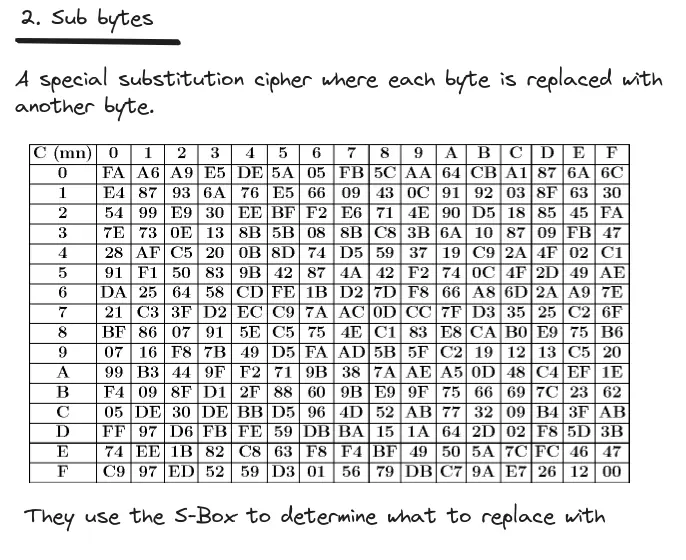
- SubBytes: Convert every byte in the state matrix with a different byte in a 16x16 lookup table (S-Box)
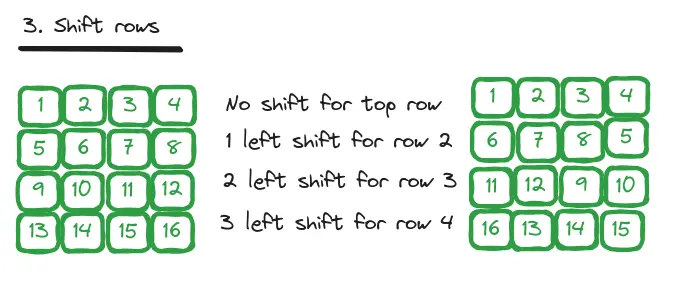
- ShiftRows: ensures columns are encrypted dependently
- First row in matrix remains the same
- Second row shift one column left
- Third row shift two columns to left
- Fourth row shift three columns by left
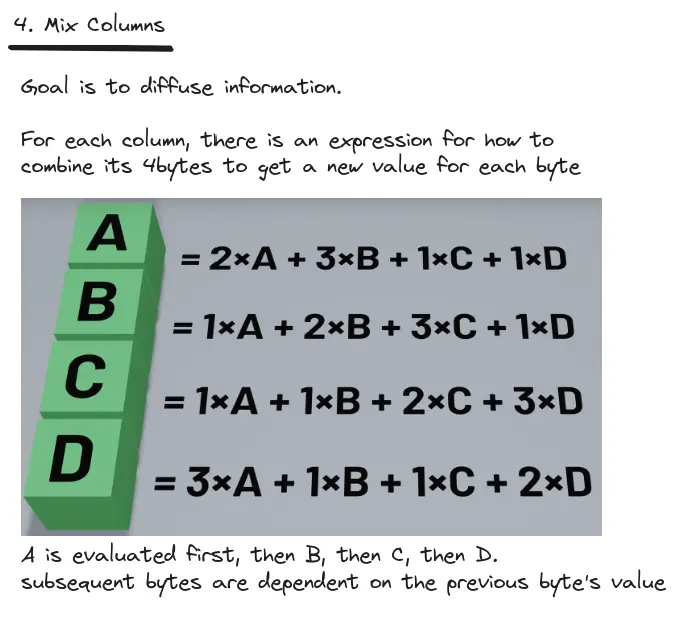
- MixColumns: Matrix multiplication of a Rijndael Galois Field
Decryption Process
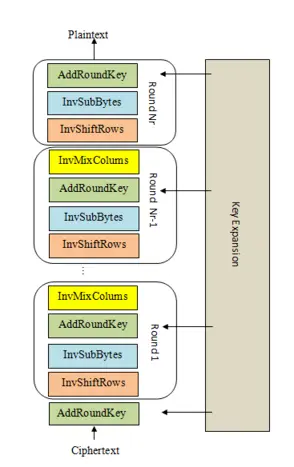
- Our input is split into 16-byte block, each block is converted into a Matrix
- Key Expansion: The 16-byte key segments is turned into number of Round Key which are also matrix
- if AES-128
- if AES-192
- if AES-256
- Set the current state to the 16-byte input matrix
- Repeat for rounds:
Diagram